FREQUENTLY ASKED QUESTIONS
Our Office hours are Monday- Friday 10am - 7pm EST We are CLOSED ON WEEKENDS & ALL LEGAL HOLIDAYS. Best Way to Contact US - Is Via our Chat Service - Visit Button at Bottom of this Page. Our Chat service allows text messages and emails to be translated between our customers in real time. Most Commonly Questions can be Answered here. You can track your orders, ask questions etc... Our Staff is available for you. Phone: 845.675.7505 - E-Mail: info@sureshotbooks.com
NO SOME FACILITIES ONLY ALLOW PUBLICATIONS DELIVERED FROM THEIR LIST OF APPROVED VENDORS ! PLEASE CONTACT THE FACILITY FOR THEIR LIST OF VENDORS. But YES we are APPROVED at most Federal Prisons, State Prisons, Correctional Facilities, Detention Centers, Sheriff's Dept., County & City Jails Etc...... We are a FULL SERVICE Publishing company - Not a Third Party Company. Please contact the facility's Mailroom with any questions or concerns and to be assured your order will be received from us.
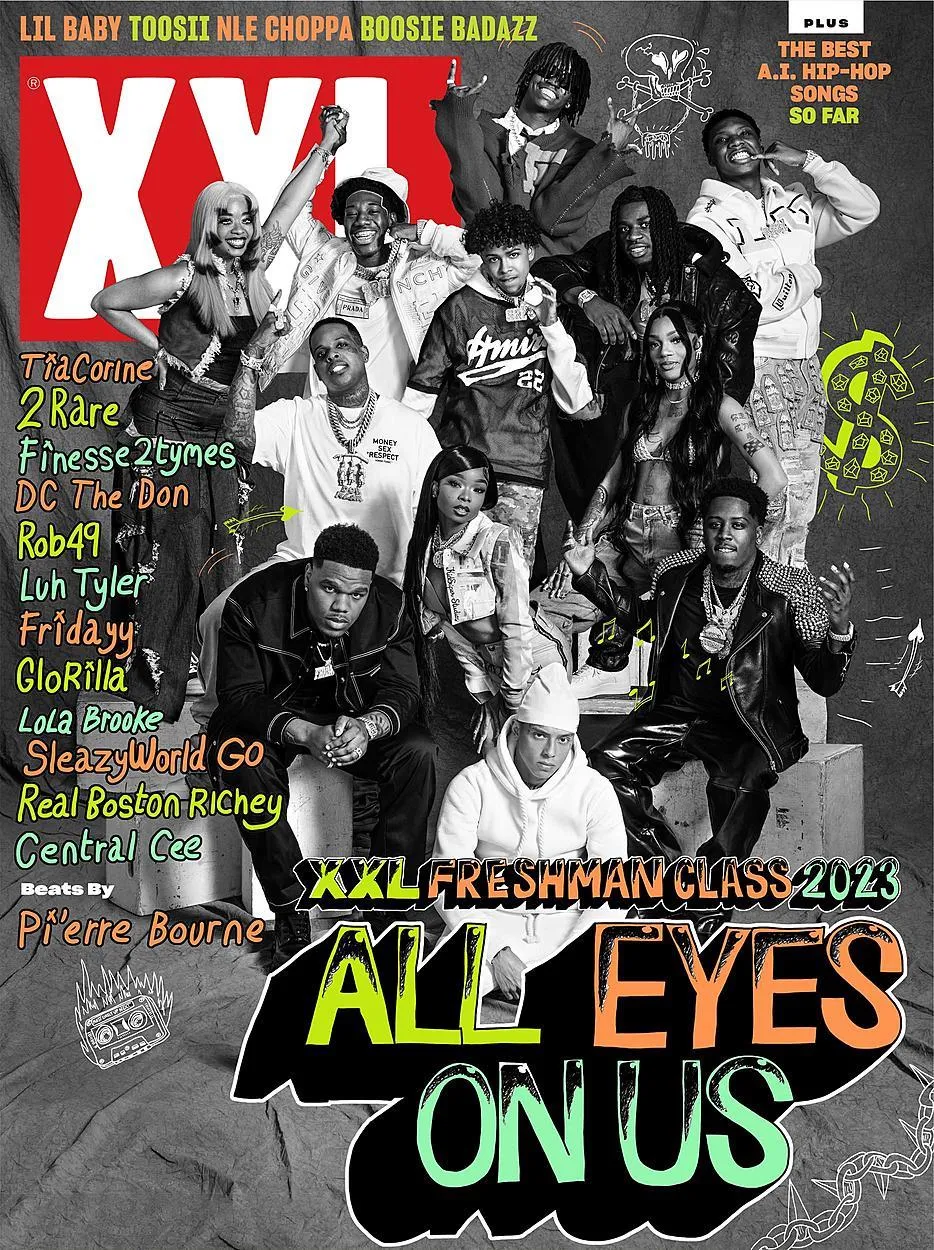
REFUND will be issued if a book is unavailable or out of stock. PLEASE NOTE: CUSTOMER IS RESPONSIBLE FOR ALL SHIPPING & HANDLING FEE'S - BOTH GOING AND IF ITEMS ARE RETURNED BACK TO US. NO REFUNDS/NO CREDITS will be issued for returned item(s) that are damaged and not in original condition as shipped. Examples include: Damaged Cover, Bent Pages, Staples in Pages, Markings, Holes, Name placed on items etc. PLEASE NOTE BEFORE PURCHASING NEWSPAPER * MAGAZINE SUBSCRIPTIONS * SINGLESHOT MAGAZINES: ALL SALES ARE FINAL! NO REFUNDS, CREDITS OR CANCELLATIONS. SureShot Books Publishing LLC cannot offer refunds, credits, or cancellations for newspapers or magazine subscription ONCE purchase. Newspaper & Magazine Publishers allow for a change of address ONLY. All newspaper & magazine subscriptions are delivered by United State Postal Service (USPS) PLEASE CHECK WITH FACILITIES BEFORE ORDERING
Yes / No Yes some Correctional Facilities accept Hardcover Books We ask you to PLEASE contact the Facilities Mailroom and ask if Hardcover Books are allowed before ordering. If Not books will be rejected and returned No - Most do Not - Most of our Selections are Paperback - To determine selection look for Binding Type in description.
Any question?
If we still haven't answered your question, you can contact us below and we will get back to you as soon as possible.
Our collections
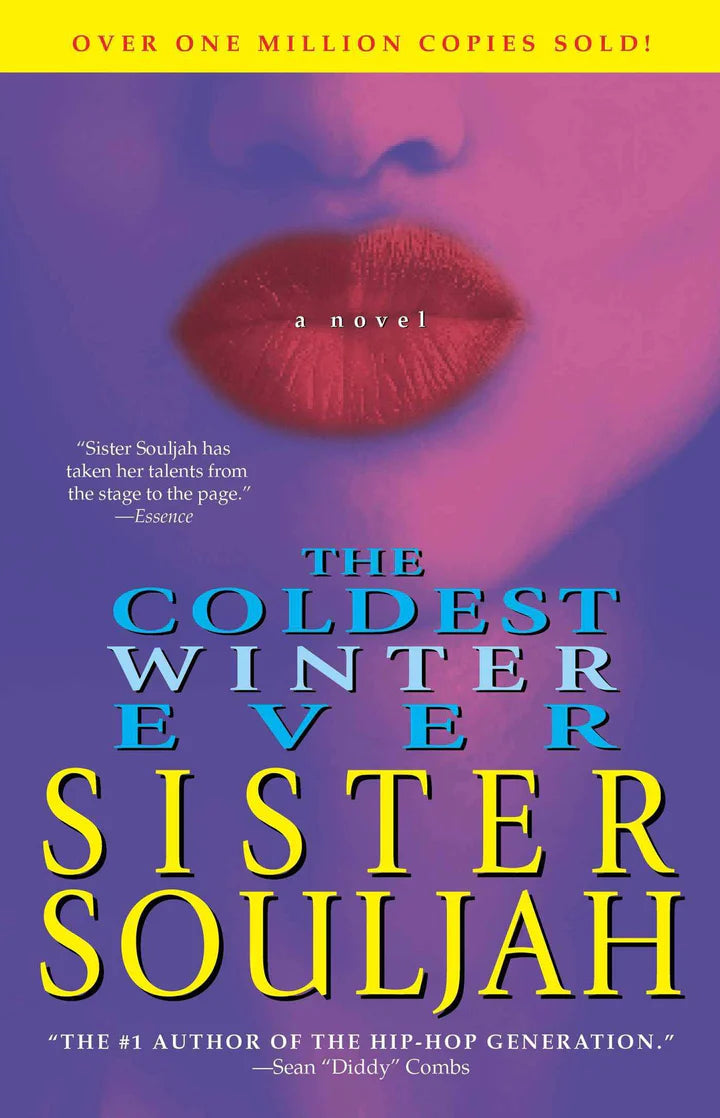
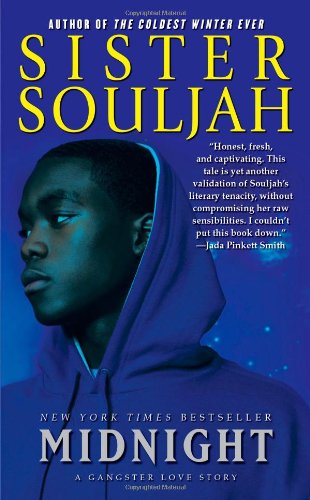
View allBEST DEALS UNDER $10
Best Sellers


Videos